Seller Central vs Solution Provider Portal
Olivia Reyes

Amazon Seller Central User Permissions vs. Amazon Solution Provider Portal: Which Structure Actually Protects Your Brand?
Many sellers still grant agencies access by adding them as secondary users in Seller Central and assuming it will not create account-association risk later.
For years, that approach was common. Today, it deserves a more cautious, governance-first review because access patterns, shared credentials, and third-party workflows can contribute to enforcement scrutiny if other risk signals are present.
The shift from Amazon Seller Central user permissions to Amazon Solution Provider Portal is not just cosmetic. It changes how you authorize third parties, how access can be scoped, and how cleanly you can document who has access to what.
For operators managing meaningful revenue, this decision is not administrative. It is a control design choice with real operational consequences.
Below is a strategic comparison for experienced sellers focused on suspension risk, data control, and scalable access governance.

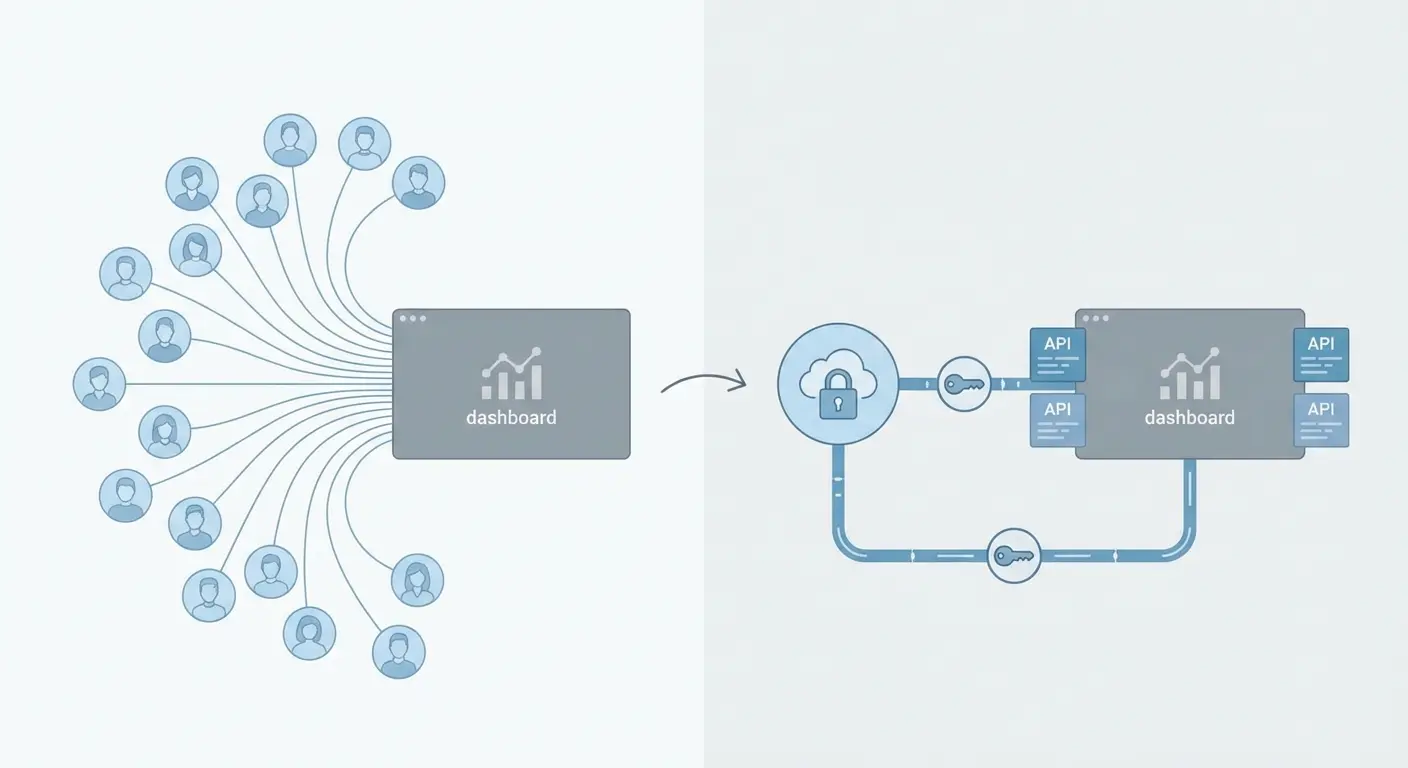
Two Access Models That Look Similar but Behave Differently
Both systems let external parties support your Amazon operation. Structurally, they are not equivalent.
Traditional Seller Central Secondary Users
This is the legacy model most sellers know.
You go to Settings, then User Permissions, and invite someone by email. If you have ever searched how to add a user to Amazon Seller Central, you have used this workflow.
The invited person becomes a secondary user, and you toggle permissions for areas such as inventory, orders, advertising, reports, and administrative settings depending on what Amazon makes available in your region and account type.
This model was designed for internal teams, then widely adapted for agencies, freelancers, and contractors.
Amazon Solution Provider Portal (SPP)
Amazon Solution Provider Portal is Amazon’s framework for third-party providers who connect through approved integration and authorization flows.
Instead of only relying on a manually invited user login, you can authorize a provider relationship and scope what the provider can access based on the service and integration. In many cases, this is implemented through permissions and tokens tied to Selling Partner API, rather than broad UI access.
This is a common foundation for Amazon SPP permissions setup and often goes hand-in-hand with modern third-party tooling.
The Core Structural Difference
When you compare Amazon secondary user vs authorized partner, the difference is not just the interface.
Key distinctions include:
Individual login access vs provider relationship and scoped authorization
Broad console access vs task-scoped or API-scoped access, when available
Manual user governance vs structured third-party governance and revocation paths
These differences influence how cleanly you can control access, audit it, and remove it.
What Actually Matters When Choosing an Access Model
Before choosing a model, define the criteria that matter in real operations:
Risk surface that can contribute to Amazon related accounts suspension
Ability to reduce signals that could help prevent Amazon account linking when multiple accounts and vendors are involved
Your ability to protect Amazon customer PII
Control over financial and operational data exposure
Scalability across agencies, tools, and marketplaces
Everything below maps to these priorities.
Legacy Secondary Users: Flexible, Familiar, and Easier to Mismanage
Where This Model Still Works
For internal staff, Amazon Seller Central user permissions remain practical.
Strengths:
Fast setup
Clear access checkboxes for many workflows
Direct console visibility for daily operations
No dependency on provider registration
If you are adding an in-house operations manager or employee, secondary users can be appropriate.
Where It Breaks Down
The system becomes more fragile when used for external agencies.
Over-permissioning is common. To avoid bottlenecks, sellers often grant broad permissions that expose sensitive settings, reports, and operational controls.
Amazon ghost users security risk is also common in mature accounts. Former contractors and agencies sometimes retain access longer than intended, especially when multiple team members rotate through an engagement.
Account-association risk can compound over time. Amazon does not publish the exact signals used to assess account relationships, and no access model can guarantee isolation. Still, shared access patterns, reused credentials, and overlapping operational fingerprints can become part of a broader risk picture, especially if one of the connected parties is involved in policy violations.
That is where Amazon related accounts suspension becomes painful. Holds, listing removals, or review requests can happen quickly, and resolving related-account concerns often requires documentation and a clear narrative of separation and control.
Costs and Operational Burden
The direct monetary cost is usually zero.
The governance cost is not:
Periodic user audits
Permission reviews after role changes
Coordinating access across ad accounts and related tools
Offboarding processes that must be executed consistently
This model often scales poorly when you manage multiple brands, multiple agencies, or multiple marketplaces.
Failure Modes to Watch
Agency receives permissions that allow changes to sensitive account settings
Former contractor retains access for weeks or months
Multiple clients share the same freelancer with inconsistent security practices
Customer data is exported and stored insecurely outside controlled systems
If you cannot confidently list every external login currently active in your account, access control is already a business risk.

The Solution Provider Portal: Structured Third-Party Access With Better Guardrails
Where SPP Helps Most
Amazon Solution Provider Portal is designed to formalize third-party relationships.
Strengths:
Clear third-party authorization framework
Scoped access in many API-driven workflows
Better separation between internal console users and external service providers
Cleaner auditability for enterprise governance
Practical alignment with Amazon Selling Partner API migration efforts
When you hire Amazon authorized partner providers who use structured authorization, you are typically reducing the need for broad console access while making the relationship easier to document.
Data Governance Improvements
SPP can support a tighter approach to data access. Depending on the integration and the scopes you authorize, a provider may not need the same breadth of console visibility that a secondary user would have.
This is particularly relevant when you need to protect Amazon customer PII. Even when order operations require some buyer information, the goal should be minimization, controlled handling, and rapid revocation when access is no longer needed.
For brands operating internationally, stronger access governance also supports compliance programs and buyer expectations, even though your obligations will vary by jurisdiction and business model.

Operational Efficiency
Many advanced workflows are API-driven. With the right partner and scopes, SPP-connected operations can support:
Automated reporting
Inventory and catalog synchronization
Advertising and performance data pulls, where supported
Monitoring and alerting tied to account health
This often reduces the need to grant agency access Amazon through full console permissions for routine work.
Costs and Effort
For sellers, there is typically no separate platform fee to authorize a provider relationship.
The effort is in migration and cleanup:
Audit who currently has access
Align on the provider authorization method
Remove legacy secondary user access that is no longer necessary
Confirm advertising and brand-related access paths separately, since ad and brand tools can have their own permission layers
Some providers will also need to complete verification steps, which can add lead time.
Risks and Edge Cases
SPP is not friction-free.
Common issues include:
Advertising access and brand tools may still require separate permissions, depending on setup
Some service providers may not be fully equipped for Amazon Selling Partner API migration
Not every freelancer is registered or organized to work through structured authorization
Some tasks still require console access, which may mean you use both models in parallel
If a provider cannot support Amazon SPP permissions setup, treat it as a capability gap and assess whether the engagement can be structured safely.
Suspension Risk: The Real Tradeoff
Adding a user can feel like harmless administration. In practice, it creates a relationship inside Amazon’s ecosystem that must be governed.
With traditional secondary users, broad console access increases the chance of inconsistent security, lingering access, and exposure to shared operational patterns across multiple clients.
SPP can reduce reliance on shared console logins and can make third-party relationships easier to define and revoke. This supports the operational goal to prevent Amazon account linking, although no approach can guarantee that Amazon will never review accounts for potential association.
SPP does not eliminate enforcement risk. If a partner engages in policy violations, manipulative activity, or prohibited practices across accounts, Amazon may still investigate. The point is to reduce unnecessary risk created by weak access architecture.

Data Exposure and PII: The Quiet Liability
Many advanced sellers underestimate how much a broadly permissioned secondary user can see and export.
Depending on what you grant, secondary users may access:
Order information that includes buyer names and addresses
Performance and sales dashboards
Reports that expose pricing and margin assumptions
Account settings that should be restricted
If you need to protect Amazon customer PII, prefer least-privilege access, minimize exports, enforce retention rules, and ensure offboarding is immediate when engagements end. When SPP and scoped access can replace broad console visibility, it is often the safer structure.
Buyers and acquirers increasingly evaluate access controls during diligence. A clean third-party authorization model helps demonstrate mature governance.
Which Model Fits Which Seller Profile?
Secondary Users Can Be Appropriate If:
Users are internal staff with documented roles
You operate a simple account structure
You perform monthly access reviews
No external freelancers require console access
In this case, Amazon Seller Central user permissions can be a sensible default.
Prioritize SPP If:
You work with agencies, contractors, or multiple service providers
You operate multiple seller accounts or brands
You are scaling across marketplaces
You rely on software tools that require structured authorization
You want cleaner governance around potential account association risk
If these apply, Amazon Solution Provider Portal is often the more defensible model for third-party access.
Conditional Recommendation
For internal employees, use Amazon Seller Central user permissions, keep permissions tight, and remove access immediately when roles change.
For third parties, prefer structured authorization through Amazon Solution Provider Portal when available. Specifically:
Require agencies to provide the appropriate authorization flow rather than relying on long-term secondary user access
Remove legacy secondary users once they are no longer necessary for operational tasks
Audit advertising and brand tool permissions separately
Review third-party access quarterly and after every engagement change
If you need to grant agency access Amazon, do it with least privilege, documented purpose, and a defined offboarding date.
Side-by-Side Snapshot
| Dimension | Secondary Users | Solution Provider Portal |
|-----------------------|--------------------------------------------------|--------------------------------------------------|
| Identity Model | Individual login | Provider relationship and authorization |
| Linking Risk | Can increase exposure if mismanaged | Often reduces reliance on shared logins |
| PII Exposure | Can be broad if permissions are broad | Can be minimized through scoped access |
| Revocation | Manual user removal | Authorization or token revocation |
| API Alignment | Not the primary design | Often aligned to SP-API workflows |
| Enterprise Readiness | Depends on governance maturity | Typically stronger governance patterns |
The Strategic Bottom Line
The choice between Amazon secondary user vs authorized partner access is about governance, not convenience.
Secondary users can work well for internal teams but become fragile when used as a default for third parties.
Amazon Solution Provider Portal supports a cleaner third-party model, better scoping in many workflows, and stronger auditability. Done correctly, it reduces avoidable exposure that can contribute to security gaps, data leakage, and account-association complications.
If your brand is meaningful in scale, treat access architecture like any other risk control. Design it early, document it, and keep it auditable.


